Security
It is important to ensure that POST requests to your endpoints are from Hotel Manager. There are two different methods you can employ to validate webhooks sent to your API.
1) Token Validation
You can specify a token on your endpoint to validate incoming requests.
Let's say that you have an endpoint with the following structure:
https://api.your-app.com/webhook
It is possible to add a token to the endpoint. This can be done before creating a subscription.
https://api.your-app.com/webhook/eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiaWF0IjoxNTE2MjM5MDIyfQ.SflKxwRJSMeKKF2QT4fwpMeJf36POk6yJV_adQssw5c
The example above uses a JWT. When a request is sent to your endpoint, you can validate the secret in the JWT to ensure that the request is secure.
2) HMAC Validation
You also have the option to verify webhooks using a signature in the request header.
To get started you need to generate a API Key from your Dashboard.
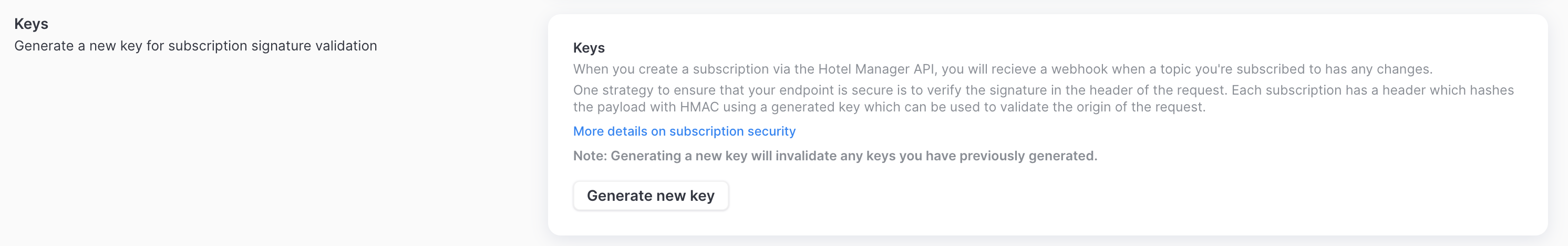
You can generate a new API Key at an time, however this will make any previous keys invalid. You need to save this key in a safe place, usually in your environment variables.
Hotel Manager sends the following header in each request when an API Key has been generated.
{
"X-Hotel-Manager-Signature": "t=1654168385,v1=e020e234ebd344e38e669c4b928490b4bb9bd01107cdae13ff6f08398d52039d"
}
Validate signature
The signature is split into 2 parts (1) the timestamp, which is prefixed by t= and (2) the signature, which is prefixed by a scheme. Schemes start with v, followed by an integer. Currently, the only valid signature scheme is v1. Hotel Manager generates signatures using HMAC with SHA2-256.
You should ensure that the timestamp is within an acceptable tolerance. It is best practice to choose a value of less than 5 minutes.
You can generate the expected value of the signature by computing a HMAC using your API Key with the SHA256 hash function. If the signatures match the request is valid. An example in JS is given below:
const headerSignature = <string>request.headers['x-hotel-manager-signature'];
const webhookPayload = request.body;
const expectedSignature = crypto
.createHmac('sha256', process.env.HM_API_KEY)
.update(JSON.stringify(webhookPayload), 'utf-8')
.digest('hex');
if (headerSignature === expectedSignature) {
handlePayload(webhookPayload);
}